

Risk-Based Vulnerability Management
Risk Based Vulnerability Management
Is your effort spent on addressing false positives or prioritized risks?
Businesses are prone to increased attacks as the security teams are buried under tons of assessment reports and slow to identify the vulnerabilities that are key to their business. Most of the team’s precious effort is going towards addressing false positives

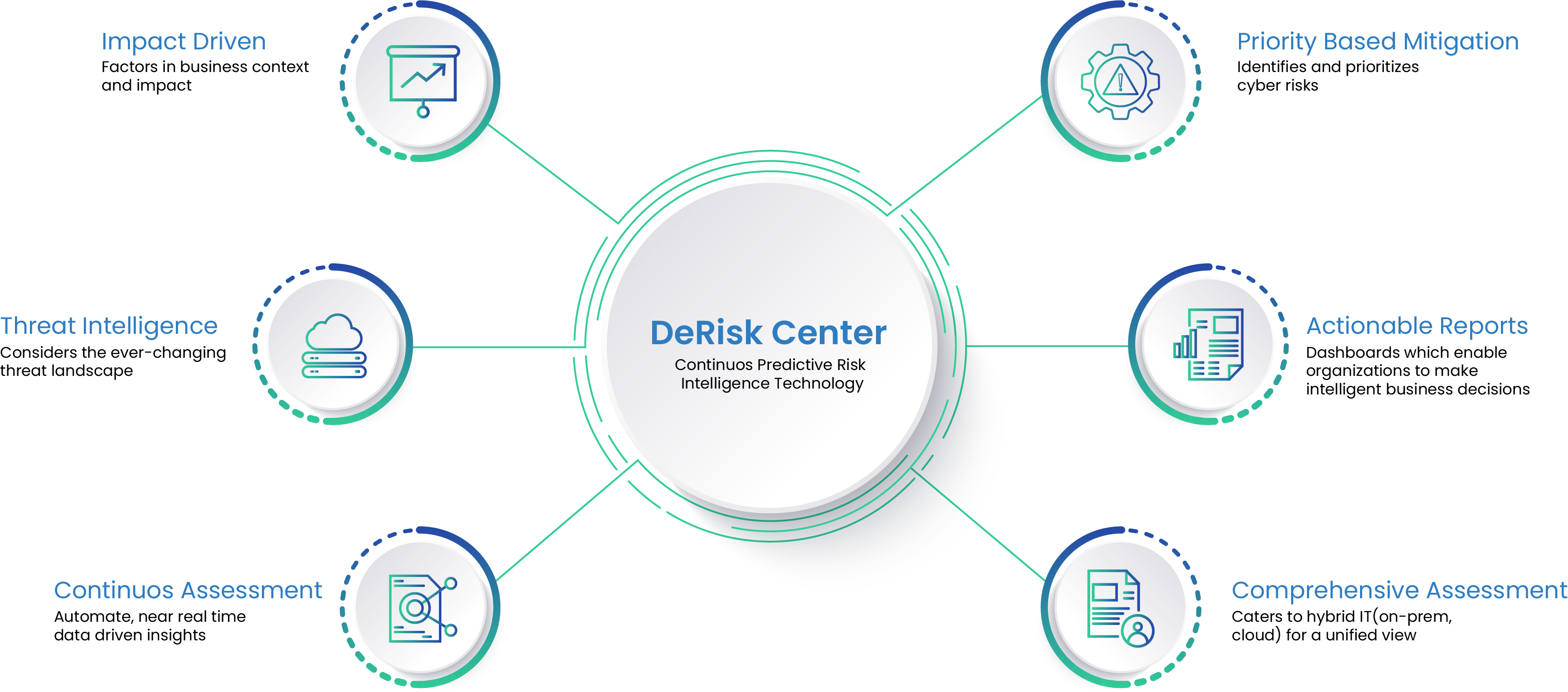
Let Seconize DeRisk Center Help Secure Your Digital Assets Using Risk Based Prioritization & Automation
Continuous Scanning Across Digital Assets & Prioritization
With Seconize you can now perform continuous scanning across all digital assets. The vulnerabilities are Prioritized based on key factors and recommendations given based on risk it poses to the organization.

Quicker Remediation
Based on the prioritized risks, resources are allocated to address the relevant issues and achieve a better security posture within days by using the auto-remediation feature.
Context driven assessment
Since each organization is unique, the solution takes into account the organization context while assessing the risk, and using inbuilt AI and ML algorithms, considers the threat to compute the risk.
Seconize DeRisk Center Is Packed With Features Every SMB & Enterprise Requires
01
Instant Asset On-boarding and Classification
02
Built-in or Bring your Own Scanners
03
Continuous and Contextual Risk Prioritization
04
Threat Intelligence Using AI/ML Alogirthms
Product leverages a combination of
05
In-built Workflows
Access our simple and inbuilt workflows for
06
Streamline Remediation
Holistic Risk Assessment Provides Business Alignment Across Departments
Seconize solution is unique in terms of Holistic Risk assessment, so all functions of business are aligned by having a unified view of risks of all the assets of the company,

CISO
Gain visibility across the entire organization on a real time basis
Executives
Know the security profile, the overall exposure, and the investments needed to bring the risk posture to acceptable levels

IT Team
And the IT team can get to root cause of the problem and the associated remediation
Testimonials
We had approached Seconize to undertake penetration tests and guide us on any potential security threats. We selected Seconize looking at the relevant security and technology backgrounds of its founders. They had the necessary experience and background to guide us on areas we may not be aware of. Seconize team was highly proactive and enthusiastic.
Seconize Intro to RBVM
There is a common saying
“Things which matter most must never be at the mercy of things which matter least.”
This applies very much to IT risk management and cyber security.
Most CISO, CIO heads we meet, express a common problem, which is how to overcome the increasing number of cyber security issues with limited resources and time.
Download to read more…

Copyright © 2024 Seconize Technologies Pvt Ltd. All rights reserved.


