In the mythical tales of ancient Greece, Sisyphus was condemned to an eternity of futile effort, perpetually pushing a boulder up a hill only to watch it roll back down each time he neared the summit.Especially when considering the arduous task of managing vulnerabilities without the aid of a proper risk-based vulnerability management (RBVM) system, this narrative resonates profoundly within the cybersecurity realm.
The process becomes not just a challenge but a Sisyphean ordeal, where the goal of securing the digital environment feels perpetually out of reach

The Unending Burden
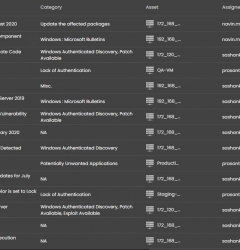
Without a risk-based approach, managing vulnerabilities is akin to navigating a labyrinth with no map. Organizations find themselves in a reactive stance, scrambling to patch vulnerabilities as they are discovered, without the ability to prioritize based on the actual risk to their environment. This method is not only inefficient but also ineffective, as critical vulnerabilities may linger unaddressed while less significant issues consume valuable resources.
The Scale of the Challenge
The digital landscape is vast and ever-expanding, with new vulnerabilities discovered daily. The National Vulnerability Database (NVD) regularly updates its list with hundreds of vulnerabilities each month. For organizations relying on manual processes or simplistic scanning tools without a risk-based framework, this presents an insurmountable challenge. Teams become overwhelmed, unable to discern which vulnerabilities pose a genuine threat from those that are less critical.
The Consequences of Misdirected Efforts
The fallout from a non-prioritized approach to vulnerability management can be severe. Critical vulnerabilities that provide easy entry points for attackers may go unpatched, leading to breaches, data loss, and significant reputational and financial damage. The effort expended on managing less critical vulnerabilities becomes a wasted endeavor, as the most dangerous risks remain unmitigated, echoing the fruitless toil of Sisyphus.
The Need for a Risk-Based Approach
A proper RBVM system transforms the Sisyphean task into a strategic, manageable process. By prioritizing vulnerabilities based on the actual risk they pose to the organization, security teams can focus their efforts where they are most needed. This approach ensures that resources are allocated efficiently, reducing the attack surface in a meaningful way. A risk-based system uses contextual intelligence, such as the criticality of the assets affected and the potential impact of a breach, to inform decision-making, turning an overwhelming flood of vulnerabilities into a prioritized list of actionable items.
Embracing Automation and Intelligence
To escape the endless cycle of vulnerability management without progress, organizations must embrace automation and intelligence. Automated RBVM systems can rapidly assess and prioritize vulnerabilities, integrating with existing security tools to provide a comprehensive view of the organization’s security posture. By leveraging threat intelligence and predictive analytics, these systems can anticipate which vulnerabilities are most likely to be exploited, allowing teams to preemptively address critical issues before they are leveraged in an attack.
Conclusion
Managing vulnerabilities without a proper risk-based system is a painful, Sisyphean ordeal, fraught with inefficiency and heightened risk. However, by adopting a risk-based approach, organizations can break the cycle, prioritizing and mitigating vulnerabilities in a way that significantly lowers their risk profile.
This strategic approach not only makes the task of vulnerability management more manageable but also more effective, ensuring that efforts are focused on the vulnerabilities that matter most.
In the realm of cybersecurity, escaping the fate of Sisyphus is possible — through intelligence, strategy, and the right tools.
Additional Learning
How to transition from Excel to RBVM tools!
https://seconize.co/blog/transitioning-from-excel/
Watch a complete tutorial on Risk Based Vulnerability Management here: https://youtu.be/h3iMaC6s2pk
Learn about Cyber Risk Intelligence in detail here:
https://youtu.be/3qCGMMcOn_o











Recent Comments